Biswap — Discovery of Critical Vulnerability on Biswap’s swap() Function

Originally published in Valix Consulting’s Medium.
On 21 Jun 2021, Valix Consulting has found a critical vulnerability issue on the swap function of Biswap. After our investigation, we contacted Biswap to inform the issue right away. And, the issue has already been resolved before we publish this report. You can find the issue details below.
The remaining of this report is organized as follows.
-
Vulnerability Details
-
Possible Attacks
-
Proof of Concept
-
Recommended Remediation
-
Patched Code
-
Summary
Vulnerability Details
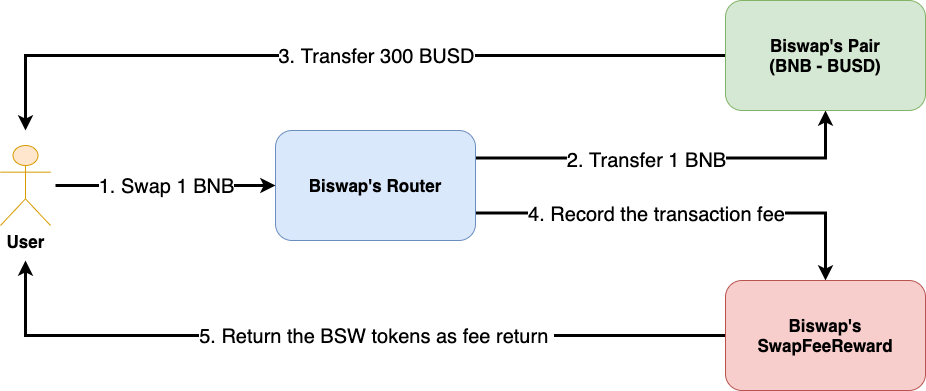
Figure 1. Biswap’s transaction fee mining mechanism
Ideally, Biswap has a transaction fee mining mechanism, as depicted in Figure 1. Every swap transaction on Biswap will have to pay a trading fee like other swap platforms. However, Biswap incentivizes users to swap on its platform by converting the trading fee to users’ fee return in the form of its native token — BSW.
For example, a user submits a transaction for swapping 1 BNB to Biswap’s Router (Step 1). Biswap’s Router transfers the user’s 1 BNB to Biswap’s Pair (Step 2). Later, Biswap’s Pair swaps 1 BNB for 300 BUSD to the user (Step 3).
Next, Biswap’s Router records the user’s transaction fee to Biswap’s SwapFeeReward (Step 4). Finally, the user can withdraw their fee return in BSW tokens (Step 5).
In Biswap, 100 million BSW tokens are allocated for the transaction fee mining. When compared to BSW’s total supply of 700 million tokens, the allocated 100 million tokens for the transaction fee mining considers the enormous portion.
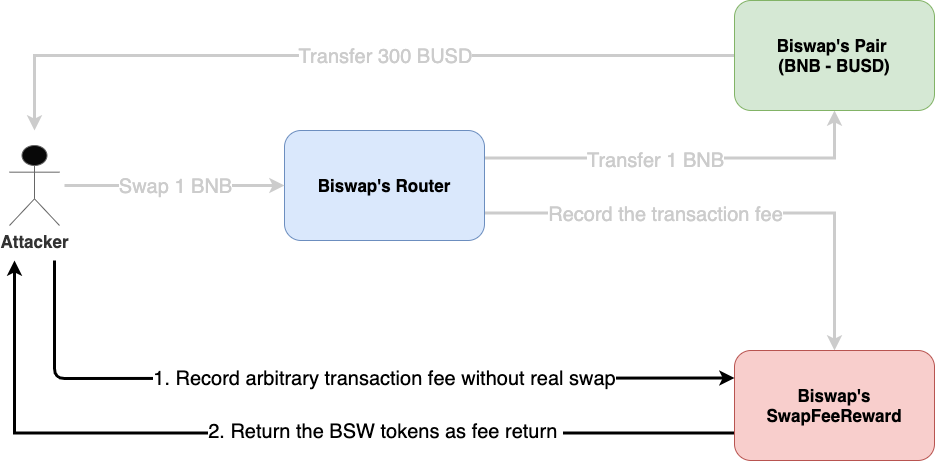
Figure 2. An attacker can bypass the Router and mint BSW tokens for free
We found the critical vulnerability issue on the swap function of Biswap’s SwapFeeReward contract. This issue allowed the attacker to bypass the Biswap’s Router and execute transactions for recording arbitrary transaction fees without requiring the real swap, as shown in Figure 2.
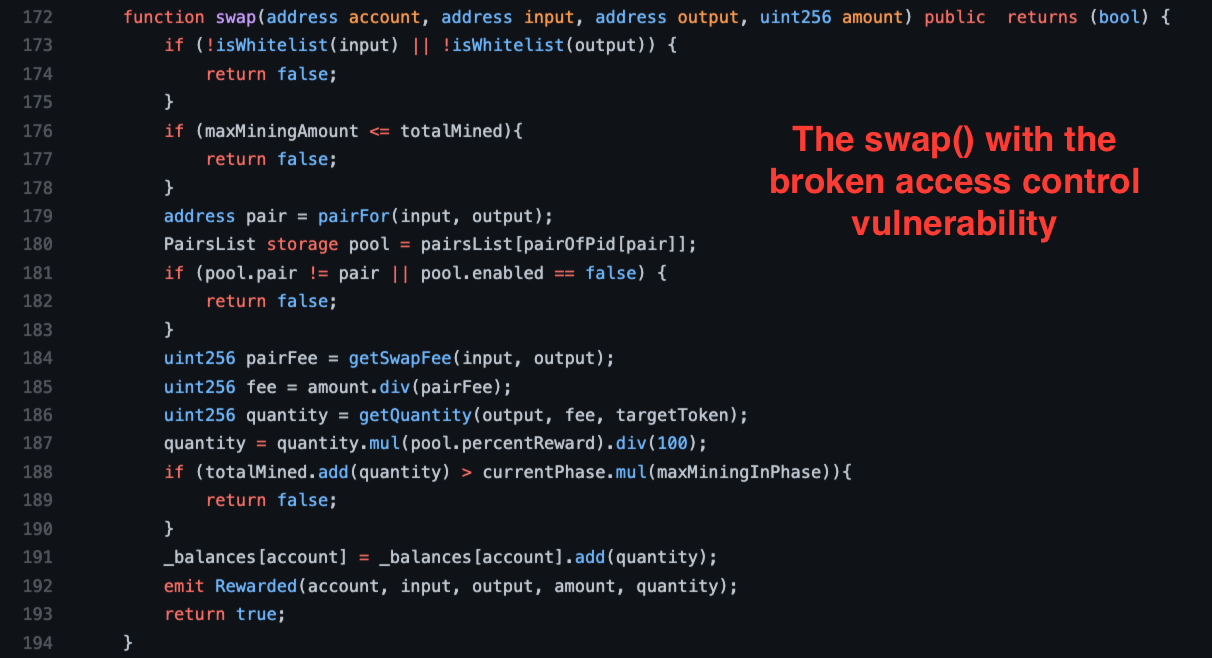
Figure 3. The associated swap function of Biswap’s SwapFeeReward contract
Figure 3 shows the swap function, a part of the transaction fee mining mechanism used by the Biswap platform. Typically, Biswap’s Router would execute this associated function after a user swaps their tokens on the platform to record the user’s fee return.
However, we discovered that there was a broken access control against the considered swap function. That is, the swap function allowed anyone to execute externally without requiring any system privilege.
Possible Attacks
-
An attacker can drain a total of 100 million BSW tokens allocated for the transaction fee mining with no actual trading fee to pay
-
An attacker can impersonate any user’s transaction by invoking the
swapfunction and passing the victim’s address as an argument
Proof of Concept
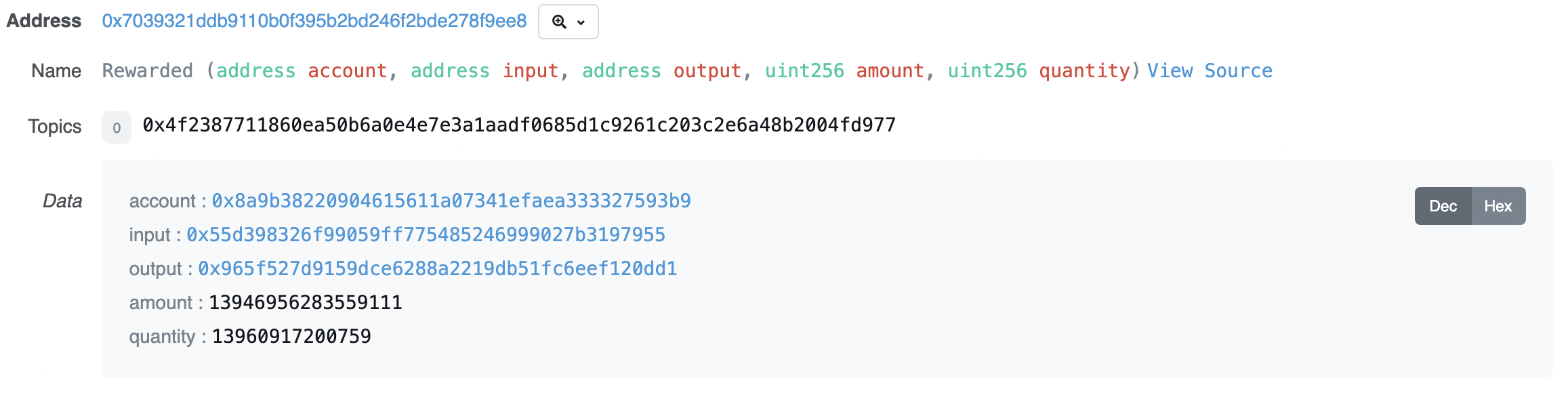
Figure 4. We could produce the PoC attack
We could produce the proof of concept attack by directly calling the swap function, as illustrated in Figure 4. You can find the transaction here.
Specifically, we tried to prove the possibility of the attack by calling the swap function to exchange 0.01394695628 BUSD for some BSW tokens. This exchange amount was considered a small volume that would neither harm the target Biswap’s transaction fee mining system nor deflate the price of the BSW token anyway. As a result, we gained the desired fee return, quantity: 13960917200759, with no real swap.
Recommended Remediation
The swap function needs to verify the caller’s identity and allow only the platform’s smart contracts to invoke to remediate the attacks.
Additional recommendation
Rename the swap function as the function’s name misleads its functionality.
Patched Code

Figure 5. The patched swap function
After our contact, the developer of the Biswap has fixed the reported issue. Figure 5 shows the patched swap function. As you can see, the onlyRouter modifier was attached to the swap function. The modifier, therefore, makes sure that only the Biswap’s Router will be able to execute the swap function successfully. You can examine the patched code from Biswap’s repo.
Summary
Valix Consulting has found a critical vulnerability issue on the swap function of Biswap’s SwapFeeReward contract. We consider this issue critical because it allowed an attacker to drain up to 100 million BSW tokens, which is more than 14% of the BSW token’s total supply.
After the discovery of this issue, we contacted the Biswap platform. And, the developer of the platform fixed the associated swap function already.
Author Details
Phuwanai Thummavet (serial-coder), Lead Blockchain Security Auditor and Consultant | Blockchain Architect and Developer.
See the author’s profile.
About Valix Consulting

Valix Consulting is a blockchain and smart contract security firm offering a wide range of cybersecurity consulting services. Our specialists, combined with technical expertise with industry knowledge and support staff, strive to deliver consistently superior quality services.
For any business inquiries, please get in touch with us via Twitter, Facebook, or info@valix.io.
Originally published in Valix Consulting’s Medium.